In recent Oracle Identity Analytics versions, risk summary can be associated to all the values such as accounts, attribues, entitlements, role, policies yarda yarda yarda. Here are the steps on how to complete this
Enable Risk Summary Maintenance
Firstly, you need to enable the risk summary job
Line 190, from...
<!--ref bean="riskSummaryMaintenanceJob"/-->
to...
<ref bean="riskSummaryMaintenanceJob"/>
Line 230, from....
<!--ref bean="riskSummaryMaintenanceJobTrigger"/-->
to...
<ref bean="riskSummaryMaintenanceJobTrigger"/>
Trigger risk Summary Maintenance Job
By default, the risk Summary Maintenance job is executed with the cron expression, '0 0 2,13 * * ?', which means every day it's executed @ 2am and 1pm, I have no idea why these time were selected over other times! Instead, if your database is small (i.e. <10,000 users) I would propose to execute this every 5 or 10mins.
Within line 1106 within the jobs.xml file, Change the following...
0 0 2,13 * * ?
to...
0 0/5 * * * ?
This will ensure the risk summary is executed once every 5 mins.
Note: Cron Maker.com is useful if you wanted to create your own cron expression.
Select your risk summary
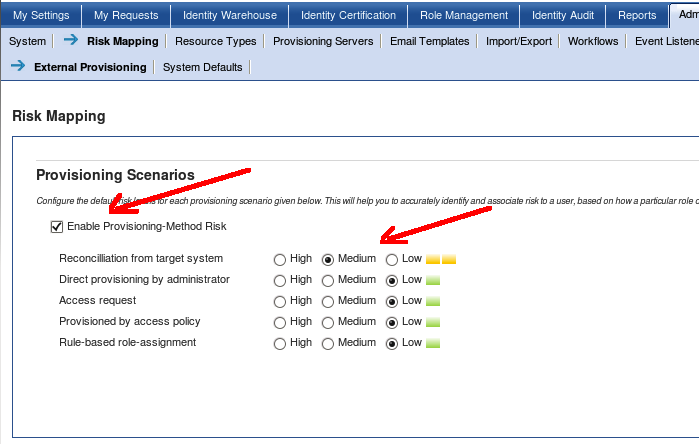
Within OIA, go to Administration --> Risk Mapping --> External Provisioning to configure the risk associated to the scenarios. The assignment is completely up to you.
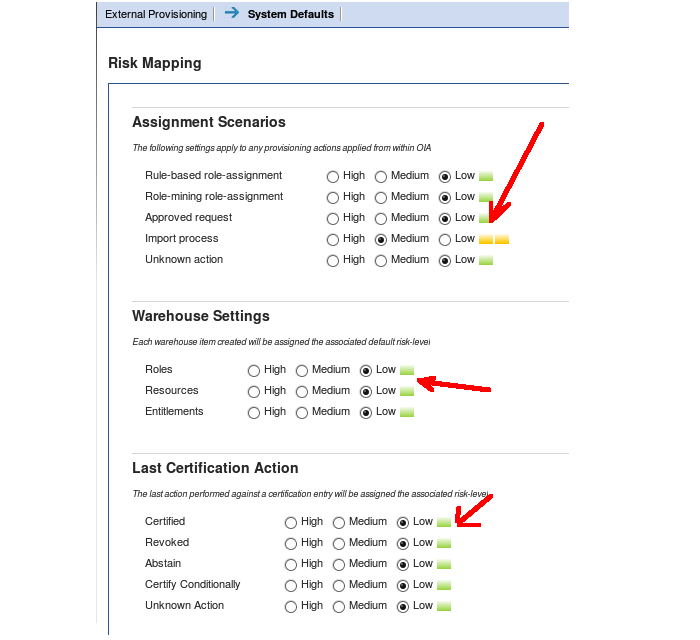
If you click the System Default tab, you can elaborate further on the risk associated to the Identity warehouse variables. Once you've selected your risk levels, click Save.
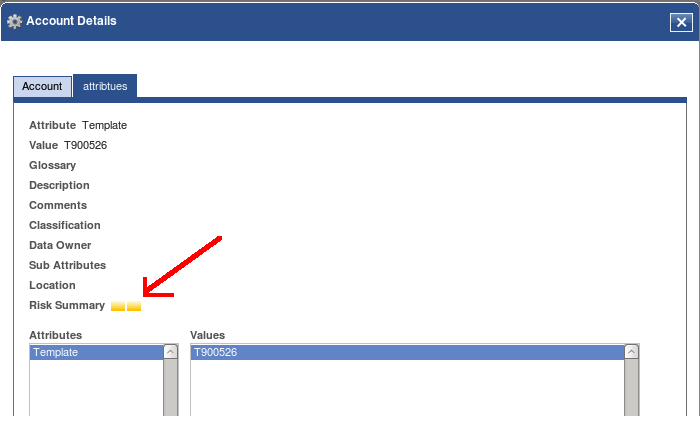
You need to ensure that you restart the application server for the changed within the xml to take effect. Once you've done that, wait around 5 mins (or whatever cron expression you used) and click on the user, accounts, attributes and attributes to see the risk assignment.
About the author
 Daniel is a Technical Manager with over 10 years of consulting expertise in the Identity and Access Management space.
Daniel is a Technical Manager with over 10 years of consulting expertise in the Identity and Access Management space.Daniel has built from scratch this blog as well as technicalconfessions.com
Follow Daniel on twitter @nervouswiggles
Comments
Other Posts
AS I was migrating my environment into an S3 environment, I wanted to leverage off the SES services that AWS provide, more specifically, to leverage the off the SMTP functionality by sending an email via PHP
Read More...
The WeMos D1 is a ESP8266 WiFi based board is an extension to the current out-of-the-box library that comes with the Arduino installation. Because of this, you need to import in the libraries as well as acknowledging the specific board. This process is highly confusion with a number of different individuals talking about a number of different ways to integrate.
Read More...
NameID element must be present as part of the Subject in the Response message, please enable it in the IDP configuration.
Read More...
For what I see, there's not too many supportive documentations out there that will demonstrate how provision AD group membership with the ICF connector using OpenIDM. The use of the special ldapGroups attribute is not explained anywhere in the Integrators guides to to the date of this blog. This quick blog identifies the tasks required to provision AD group membership from OpenIDM to AD using the LDAP ICF connector. However this doesn't really explain what ldapGroups actually does and there's no real worked example of how to go from an Assignment to ldapGroups to an assigned group in AD. I wrote up a wiki article for my own reference: AD group memberships automatically to users This is just my view, others may disagree, but I think the implementation experience could be improved with some more documentation and a more detailed example here.
Read More...
In the past, the similar error occurred though for the Oracle Identity Management solution. invalidcredentialexception remote framework key is invalid Because they all share the ICF connector framework, the error/solution would be the same.
Read More...
org.forgerock.script.exception.ScriptCompilationException: missing ; before statement
Read More...
ForgeRock IDM - org.forgerock.script.exception.ScriptCompilationException: missing ; before statement
Read More...
When performing the attempt of a reconciliation from ForgeRock IDM to Active Directory, I would get the following error
Read More...
In the past, the similar error occurred though for the Oracle Identity Management solution. invalidcredentialexception remote framework key is invalid Because they all share the ICF connector framework, the error/solution would be the same.
Read More...
During the reconcilation from OpenIDM to the ICF google apps connector, the following error response would occur. ERROR Caused by com.google.api.client.auth.oauth2.TokenResponseException 400 Bad Request - invalid_grant
Read More...

